What is Cyber Extortion
Cyber Extortion is a felony where cybercriminals commit extortion online using threats, blackmail, or ransomware to demand money, data, or favors, often exploiting victims' fear and vulnerability.

Table of Contents
Cyber Extortion Definition
Extortion is a criminal act of obtaining money, services, or something of value through intimidation, threats, or coercion and, in most cases, executed physically. Cyber Extortion is said to be the digital approach where criminals force their victims to comply using online threats.
These criminals, otherwise called hackers, set their extortion online plans in motion by exploiting weak security systems or manipulating their prey through phishing and social engineering tactics to gain access to sensitive data to use as leverage.

Cyber Extortion Statistics
Cyber extortion is a growing threat, affecting individuals and businesses worldwide. Attackers use tactics like ransomware and sextortion to demand payments, often causing significant financial and emotional damage. Staying informed about the latest statistics can help you understand the scale of the problem and take preventive measures to protect your digital assets and personal information.
813M
Global ransomware payments in 2024, a 35% decrease from 2023.
71%
Organizations that experienced an extortion or ransom DDoS threat in 2023.
25%
Ransomware’s share of all cyber incidents in 2024.
$8M
Average ransom demand in 2023, up from $5M in 2020.
Types of Cyber Extortion
Dating App Sextortion
Dating apps have done more harm than good globally. They have been a bridge for scammers to extend their reach, identify potential victims, and lure them into sharing intimate content. Once obtained, they demand money, threatening to expose the images or conversations. Warning signs include excessive flattery, quick emotional attachment, and immediate requests for explicit content.
Webcam Sextortion
Perpetrators carry out this extortion scam by tricking victims into engaging in sensual video calls and recording them without their consent. Afterward, they demand money or further explicit content under the threat of public exposure. Warning signs include sudden disconnection after explicit activity or sudden webcam issues.
Revenge Porn
This sexual extortion is common amongst formal partners or acquaintances who still feel entitled to the victim and would do anything to get their attention. They threaten to leak private images or videos to humiliate, control, or extort the victim. Victims tend to notice sudden social media hacks, leaked content rumors, and threat extortion emails.
Sextortion by Organized Crime Groups
Organized crime groups of scammers form a network to trap and exploit victims worldwide. They are tech-savvy and sophisticated to operate on multiple platforms, impersonate law enforcement, and use fake legal threats to pressure victims into compliance. Warning signs include high-pressure demands and coordinated threats from multiple sources.
Deepfake Sextortion
Scammers are fond of using AI generating tools to create deepfake nude images and videos to manipulate victims with little time to meet their demands. Victims should pay keen attention to images sent, mostly AI-generated pics and non-existent videos edited to lure them.
Child Sextortion
Perpetrators often pose as mentors, peers, or influencers to exploit children who are shallow-minded and manipulate, force, or deceive them into sending explicit images and videos. Parents or guidance should watch out for signs like unexplained money transfers, secretive behaviors, and sudden distress.
How to Prevent Cyber Extortion
Protect yourself from cyber extortion by following best practices to secure your online presence. Stay vigilant, use strong passwords, and be cautious about sharing personal information. Learn how to identify threats and act quickly to minimize potential harm.
Strong Passwords
Two-Factor Authentication
Regular Software Updates
Be Cautious with Links
Backup Your Data
Report Suspicious Activity
What to Do about Cyber Extortion
-
1
Do not Panic
Online extortion scams are directed at frail and emotionally weak people, so you have to be as composed as you can be when you receive any extortion emails with threats to expose sensitive or explicit images of you.
-
2
Deactivate all Social Media Accounts
Make yourself inaccessible to perpetrators by staying off social media platforms. By doing so, you can limit access to the information within your control that is available online.
-
3
Preserve all Evidence
Be two steps ahead by taking screenshots of extortion emails, chats, messages, account details, and financial transactions, as this evidence will help local enforcement or cyber extortion agencies in investigating the extortion case.
-
4
Strengthen Your Online Security
Avoid getting hacked again by using a stronger password. Enable two-factor authentication (2FA) to make your social media accounts almost impossible to breach. Scan your devices for malware to prevent forthcoming data exploitation.
Is Extortion a Felony?
Yes, extortion is considered a felony in most jurisdictions, as it involves obtaining money, property, or services through threats, coercion, or intimidation. Felony extortion charges carry severe penalties, including hefty fines and lengthy prison sentences. The severity of the punishment often depends on factors such as the amount of money involved, the nature of the threats, and the impact on the victim. In cases of cyber extortion or sextortion, additional charges related to cybercrime and privacy violations may apply. Victims are encouraged to report extortion to law enforcement authorities, as prompt action can help mitigate the damage.

How We Can Help
Your sanity and safety matter to us! Our sextortion helpline is readily available for you to report sextortion online cases to guide you through extortion scams with confidential assistance, expert advice, and immediate action plans. Report extortion email as soon as you receive it, so we can help you track the perpetrators.
FAQ
How to deal with extortion threats
Turn off all social media notifications and deactivate the accounts temporarily. Ensure you keep a calm mind so you don't get swayed easily to fall under pressure and comply with their demands. Instead, strengthen your security, collect evidence (messages, sextortion emails, threats), and report it to law enforcement or cyber extortion agencies.
How to stop extortion?
Cease communications with the blackmailer, keep evidence and records that can be used to ascertain the perpetrators, and report the extortion case to appropriate authorities. Strengthen your security by enabling 2FA. If you feel unsafe, don't hesitate to consult legal authorities to seek protection.
What to do when someone is extorting you?
Do not panic or respond emotionally. Document every interaction as proof, avoid paying or complying and report the extortion to the appropriate authorities. If online, report it to the platform where it occurred. Consider reaching out to a lawyer or cybersecurity expert for guidance.
What to do if you receive an extortion email?
Do not indulge them by clicking links or responding with the aim of negotiating with them. If you do, you are likely to fall deeper into their traps. Instead, mark the email as spam, take a screenshot, and report the online extortion scam to law enforcement agencies, preferably the FBI's Internet Crime Complaint Center (IC3).
How to report extortion in Florida?
The Florida Department of Law Enforcement (FDLE) is keen to curb the excesses of data exploitation and online extortion cases. Gather all evidence, and seek legal help by filing an official complaint through the official Internet Crime Complaint Center (IC3) website, where you will be directed accordingly on steps to follow.
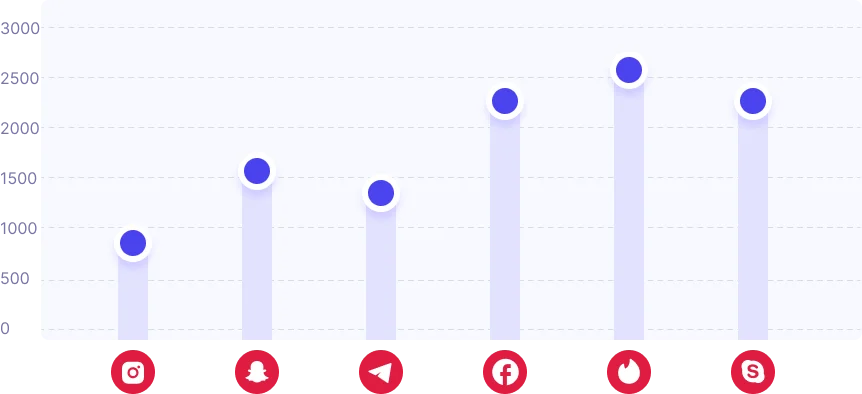
Social Media Extortion
Social media platforms are common targets for extortion scams, including sextortion. Scammers exploit users' personal information to threaten and demand payments. Stay vigilant to protect your online presence.
Sextorion Instagram
Scammers use fake profiles to gain trust and collect compromising content for blackmail.
Snapchat Sextortion
Attackers exploit disappearing messages to coerce users into paying ransom after capturing screenshots.
Telegram Sextortion
Scammers use anonymity to manipulate victims, threatening to expose private conversations or media.
Facebook Extortion
Hackers and fake profiles extract sensitive information to intimidate and extort victims.
Tinder Sextortion
Fake matches lure users into sharing explicit content, later used for extortion threats.
Skype Sextortion
Attackers record intimate video calls and threaten to leak them unless paid.