Extortion Email Scams
Are you facing extortion email scams? These threats and payment requirements sent by email are serious criminal violations, which need to be dealt with. One of such scams is sexual extortion, often referred to as extortion. Time to fight this crime. Learn how we can help.

Table of Contents
Key Takeaways
A few main takeaways referring to extortion and sextortion email scams:
- Sextortion scams often rely on threats to expose sensitive materials.
- Scammers use fake evidence to coerce their victims online.
- If you are targeted by an extortionist, never pay the ransom or talk to the scammer.
- Use cybersecurity tools to safeguard your presence on the Internet.
- Ask for professional help to fight extortion email scams as soon as possible.
What Is Sextortion Scam
Sextortion email scams take advantage of online privacy violations and prey on the defenselessness brought about by the digital age. Cybercriminals often rely on fake evidence to authenticate their activities. These include phony movies or altered images.
The psychological effects of sextortion scams can be devastating to many people, leading people to social isolation and anxiety. Victims may feel stuck thinking their reputation already has been irreversibly damaged. The key is to act swiftly to prevent the problem from spreading.

Recognize Sextortion Scam
Sextortion scams often involve threats to share intimate content unless demands are met. Scammers may pose as romantic partners or hackers. Recognizing warning signs and staying cautious online can help protect your privacy and prevent falling victim to extortion.
Fake Social Media Profiles
Threatening Messages
Demands for Money
Personal Data Leaks
Impersonation
High-Pressure Tactics
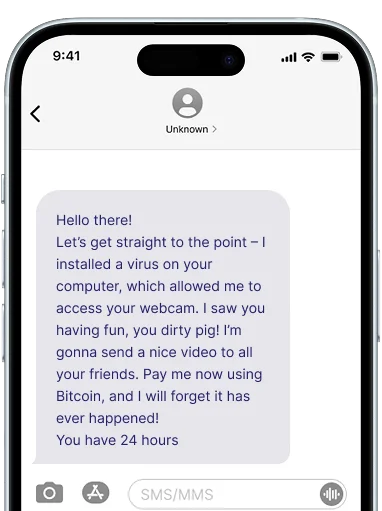
Sextortion Email Example
Take a look at an example of a sextortion email scam, which you might receive:
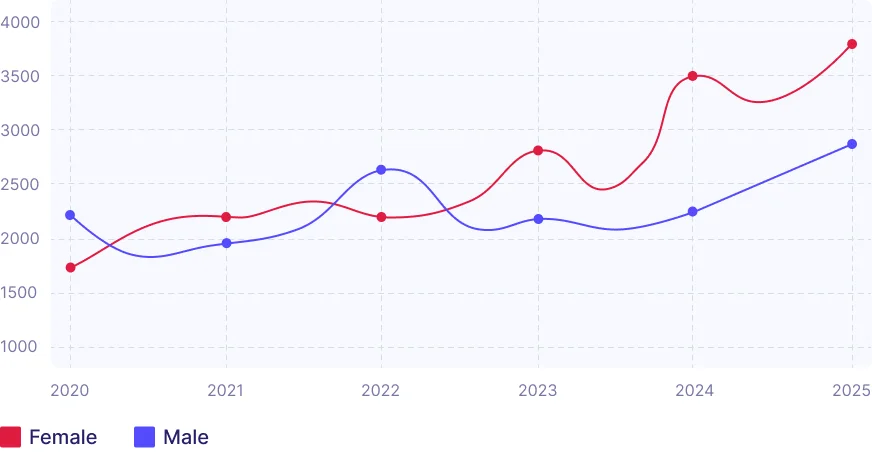
Sextortion Email Report
Between 2020 and 2025, reports of sextortion emails have significantly increased. Cybersecurity companies report thousands of incidents each year. Avoid becoming a victim of extortion scams, not fall for this malice.
How Sextortion Scams Work
Discover how extortion emails are produced, and what sextortionists do to make their scam schemes work. There are three main steps, on which they base their crimes:

Initial Contact: Extortionists send mass emails to victims, claiming they obtained sensitive data.

Threats & Demands: Criminals pressure victims to pay ransom using fake evidence.

Escalation or Silence: Victims either agree to demands or get rid of scams by reporting them.
Internet Extortion Scams
Social Media Scams
Scammers build appealing social media accounts to become trustworthy, before requesting private images or videos. Once they establish a connection with their victims, social media scams try to acquire sensitive content, and only then start making threats to disclose them to the public.
Account Hacked Scams
Hacking social media, email, or cloud storage accounts is a widespread method of Internet extortion scams. With an account hacked, scammers then threaten the victim to share vital messages or private information while demanding ransoms to restore access.
Video Call Scams
Online criminals often refer to video call scams, which seem normal at first. Scammers record these conversations while trying to get as much personal and sensitive data as possible. Then, they blackmail their victim to release the footage on the Internet.
Job Offer Scams
Fake work ads bait people into exposing personal data, such as bank account credentials or IDs, by creating false claims about simple labor or big wages. These job offer scams leave victims both emotionally and financially exposed as a result of the extortion online.
Phishing Attacks
In phishing attacks, cybercriminals fake reputable organizations, such as banks or social media platforms, in their misleading emails or messages. Scammers mislead victims into sharing personal data, such as login credentials, using phony websites, and giving them access to accounts.
AI Deepfake Sextortion
AI is revolutionizing modern cyber extortion, and deepfake sextortion schemes are in the avant-garde. Scammers can create lifelike but fake porno content relying on the victim's resemblance by using refined AI-based tech. They blackmail victims using these phony images or videos, which have the potential to destroy one’s reputation.
How to Avoid Sextortion Email
Stay vigilant against sextortion emails by recognizing common tactics and protecting your personal information. Follow these essential tips to keep your online presence secure and safeguard your privacy.
Use Strong Passwords
Enable Two-Factor Authentication
Be Cautious with Personal Information
Ignore Threatening Emails
Update Security Software
Report to Authorities
What To Do If You Got Sextortion Email
-
1
Stay Calm
Do not panic and remember that sextortion email is usually based on phony allegations. Scammers only rely on provoking anxiety and terror. Take a deep breath, and refrain from communicating with the criminal.
-
2
Do Not Pay
Paying will not ensure safety and instead could lead to further extortion online. Instead of following the scammer’s demands, ignore their false claims. Gather all proof of the extortion emails, including screenshots and timestamps.
-
3
Report the Scam
Alert fitting extortion helplines, cybersecurity specialists, or legal authorities. To report the scam, you might need all the necessary evidence of the extortion email scam, which will aid your inquiry.
-
4
Secure Your Accounts
Change your passwords, switch on two-factor authentication (2FA), and scan your devices for malware and viruses. Increase your online security by performing regular privacy settings reviews, and keeping an eye out for unusual activities.
How We Can Help
Falling victim to online extortion schemes, such as extortion email scams, can be extremely isolating. We completely understand that. That is why we offer you a 24/7 extortion helpline, which has been carefully designed to provide professional assistance in all kinds of extortion. Our staff is ready to help and will be more than satisfied to do so.
We are here to help. Our team of experts provides advice without judging you, as well as creates a safe environment for private assistance. We share tools and ways to report extortion email scammers to the correct authorities. We also share tips on how to safeguard your presence online. Get expert help now: it is just a phone call away! Do not face extortion scams on your own!
FAQ
How to stop extortion?
The first step to stop extortion online is to cease all conversations, keep evidence of everything, and never, ever pay. Paying the scammer only empowers the criminal. Stopping extortion is possible by protecting your online presence and acquiring professional assistance via an extortion helpline.
Is blackmail and extortion the same thing?
Despite blackmail and extortion being similar to each other, there are minor distinctions. Both terms refer to using threats to get something. While blackmail can involve intimidation to divulge humiliating information, regardless of financial profit, extortion commonly focuses on demanding money or property.
What to do if you receive an extortion email?
If you receive a scam extortion email, do not reply to the message. Nevertheless, do not move the email to trash, as you might need it as proof. Get professional help in reporting extortion to relevant authorities, such as the FBI's Internet Crime Complaint Center (IC3).
How to deal with extortion threats?
First of all, you must remain composed, and refrain from impulsive reactions. Keep a record of every email extortion threat. Do not interact with the scammer. Contact your reliable extortion helpline, and seek assistance on how to report extortion online. Put your online security and safety first.
How to report extortion to the police?
You can call the non-emergency number of your local police department or visit the station. Share all the specific details with the officer, as well as all evidence supporting the scam email. Prepare a statement, and allow the police to help you take the next steps in reporting the crime.